Vulnerabilities
To open this page, click Vulnerabilities (CVE) in the instance’s left-hand menu.
Attention
To fetch up-to-date vulnerability information, the system must have outbound access to https://services.nvd.nist.gov/rest/json/cves/2.0.
If access to the National Vulnerability Database (NVD) is restricted, vulnerability data will only be updated when the Platform itself is upgraded.
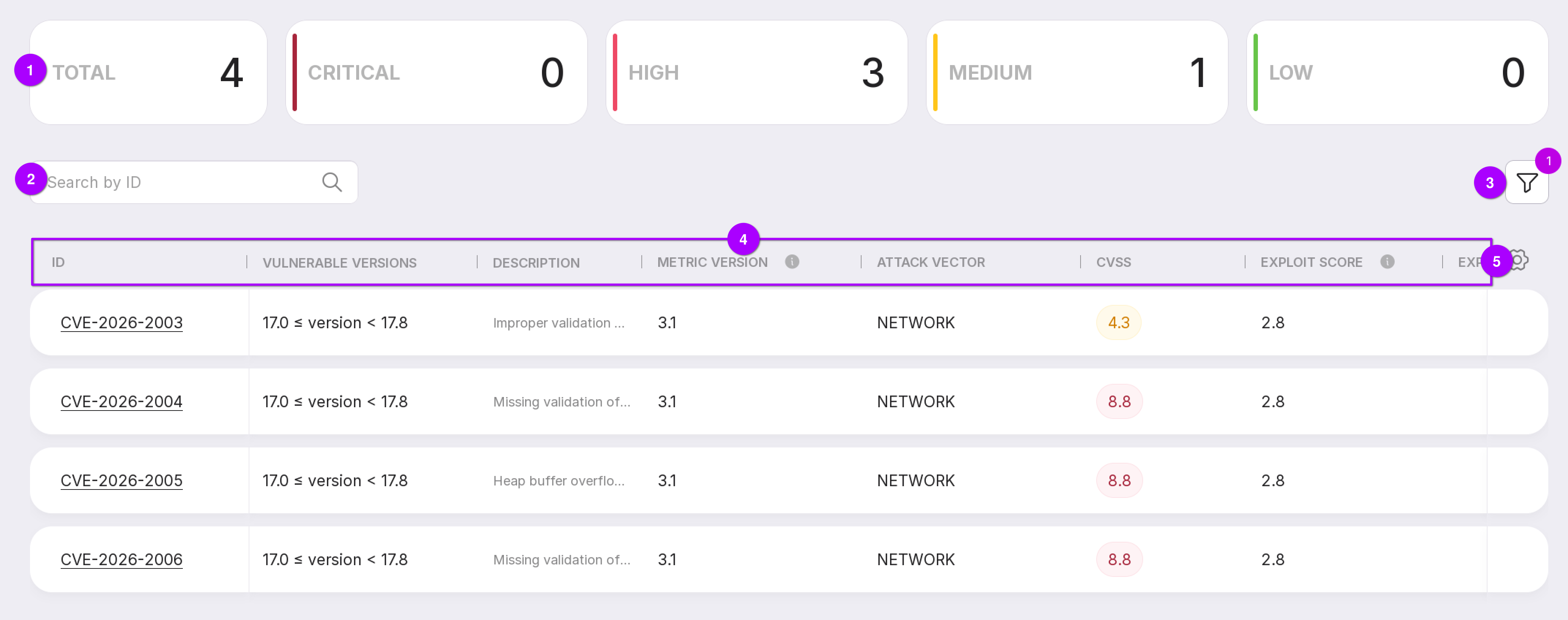
This page displays known vulnerabilities identified for the selected instance.
Number of detected vulnerabilities. In the left navigation panel, next to the section title (Vulnerabilities), you can see the count of Critical and High severity vulnerabilities.
Search field — allows you to look up vulnerabilities by CVE identifier.
Filter options by the following criteria:
Severity level: Critical, High, Medium, or Low;
Exploit availability: whether a public exploit exists for the vulnerability;
Metric version: cvssMetricV2 or cvssMetricV3 (default: cvssMetricV3).
Table customization button — allows you to configure the visible columns and layout of the table.
List of vulnerabilities, each entry containing:
ID — the CVE identifier. Clicking it opens the corresponding vulnerability details page on nvd.nist.gov;
Vulnerable versions — software versions vulnerable to this CVE;
Description — brief explanation of the vulnerability;
Metric version — v2 or v3 scoring methodology used;
Attack vector — how the attacker accesses the vulnerable system: Network, Adjacent, Local, or Physical;
CVSS score — severity rating based on the Common Vulnerability Scoring System; higher values indicate greater severity;
Exploit score — how easy it is to exploit the vulnerability (higher = easier);
Exploit — indicates whether a public exploit is available;
Recommended actions — link(s) to remediation guidance. If multiple links exist, only the first is displayed.
To view detailed information on a vulnerability, click on its row.
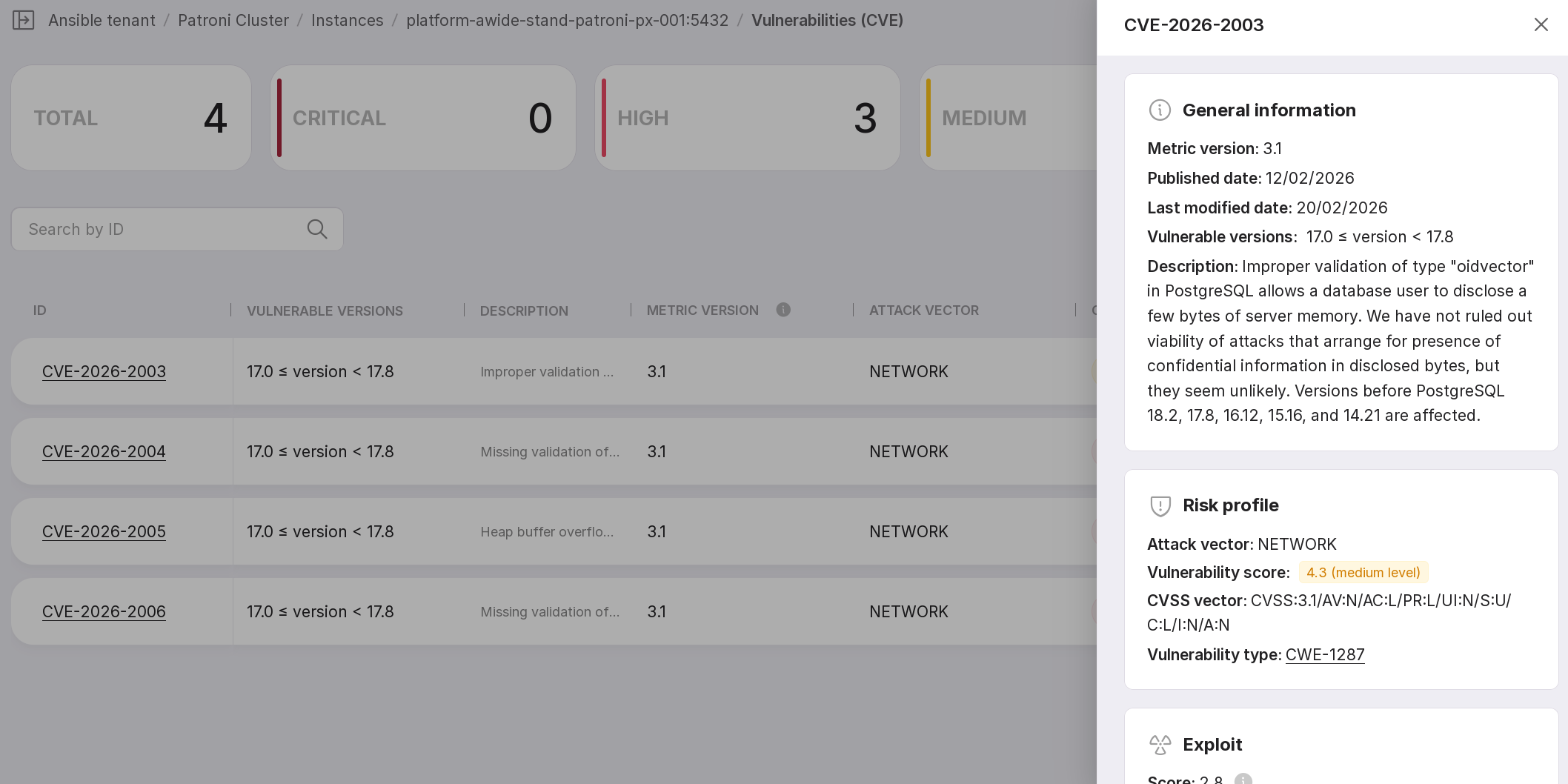
The detailed view includes the following sections:
General Information:
Metric version (cvssMetricV2 or cvssMetricV3);
Published date;
Last modified date;
Vulnerable versions;
Detailed description.
Risk Profile:
Attack Vector — proximity of the potential attacker to the target system;
CVSS Score — overall severity score;
CVSS Vector — a machine-readable string in
Metric:Value/Metric:Value/...format, showing the underlying metrics that determine the score. Metric meanings are defined in the table below;Vulnerability Type — vulnerability category as per Common Weakness Enumeration (CWE) database. Click the link to view detailed information on cwe.mitre.org.
Exploit Information:
Exploit score — a measure of how easy it is to exploit the vulnerability. The higher the score, the easier the exploitation.
Public exploit availability — whether exploit code is publicly accessible.
Recommended Actions — a list of official remediation instructions or patches.
Here is the exact translation of your provided table into English, preserving all reStructuredText (RST) markup, alignment, line breaks, and table structure:
Category |
Metric |
Value |
Description |
|---|---|---|---|
Impact Metrics |
AV (Attack Vector) |
N (Network) |
Attack can be launched remotely over a network |
A (Adjacent) |
Attacker must have access to the same local network segment (e.g., via Wi-Fi) |
||
L (Local) |
Attacker must have access to the target system itself (e.g., a local user account) |
||
P (Physical) |
Attacker must have physical access to the system |
||
AC (Attack Complexity) |
L (Low) |
No special conditions required to exploit the vulnerability |
|
M (Medium) |
Additional conditions required for exploitation (e.g., specific attack source is required) |
||
H (High) |
Exploitation requires special conditions that are difficult to create or control |
||
PR (Privileges Required) Required Privileges For cvssMetricV3 |
N (None) |
No user credentials or access privileges are required to exploit the vulnerability |
|
L (Low) |
Exploitation requires a user account with basic user-level privileges |
||
H (High) |
Exploitation requires significant privileges (e.g., administrator/root rights) |
||
Au (Authentication) Number of Number of Authentication For cvssMetricV2 |
M (Multiple) |
Attacker must authenticate at least twice, even if the same credentials are used same credentials are used |
|
S (Single) |
Attacker must authenticate once |
||
N (None) |
Authentication is not required for exploitation |
||
UI (User Interaction) |
N (None) |
User interaction is not required for exploitation |
|
R (Required) |
Exploitation requires the user to perform a specific action |
||
S (Scope) |
U (Unchanged) |
Successful attack impacts only resources managed by the same security component in which the vulnerability resides |
|
C (Changed) |
Successful attack can impact resources beyond the original
|
||
C (Confidentiality) Impact of vulnerability exploitation on system data For cvssMetricV3 |
H (High) |
Loss of confidentiality within the entire security component |
|
L (Low) |
Loss of confidentiality limited to some resources of the component |
||
N (None) |
No information disclosure |
||
C (Confidentiality) For cvssMetricV2 |
C (Complete) |
All information in the vulnerable component is disclosed |
|
P (Partial) |
Attacker gains access only to some information |
||
N (None) |
No information disclosure |
||
I (Integrity) Impact of vulnerability exploitation integrity For cvssMetricV3 |
H (High) |
Complete loss of integrity of the managed component |
|
L (Low) |
Limited integrity violation |
||
N (None) |
Integrity is not affected |
||
I (Integrity) For cvssMetricV2 |
C (Complete) |
Attacker can modify any information in the vulnerable component |
|
P (Partial) |
Attacker can modify only some information |
||
N (None) |
Data integrity is not violated |
||
A (Availability) Impact of vulnerability exploitation on system availability For cvssMetricV3 |
H (High) |
Complete loss of availability of the managed component |
|
L (Low) |
Limited loss of availability |
||
N (None) |
Availability is not affected |
||
A (Availability) For cvssMetricV2 |
C (Complete) |
Attacker can completely disable the resource |
|
P (Partial) |
Attacker can cause performance degradation or intermittent unavailability |
||
N (None) |
Availability is not affected |
||
Temporal Metrics |
E (Exploitability/ Exploit Code Maturity) |
H (High) |
Exploit code is available and can be deployed automatically |
F (Functional) |
A working, reliable exploit exists |
||
P (Proof-of-Concept) |
Proof-of-concept exploit code is available, but it is not universal and covers only one or a few specific cases |
||
U (Unproven) |
The vulnerability is known, but no proof-of-concept (PoC) or public exploit is available |
||
PD/X (Not Defined) |
Metric does not affect scoring and will be ignored |
||
RL (Remediation Level) Remediation Availability |
OF (Official Fix) |
A complete fix is available from the vendor as an update or patch |
|
TF (Temporary Fix) |
A temporary workaround exists that partially mitigates the vulnerability impact |
||
W (Workaround) |
An unofficial mitigation or protection mechanism from third parties is available |
||
U (Unavailable) |
No fix is available, or the proposed solution cannot be applied |
||
PD/X (Not Defined) |
Metric does not affect scoring and will be ignored |
||
RC (Report Confidence) Report Confidence |
C (Confirmed) |
Vendor has officially confirmed the vulnerability |
|
PD/X (Not Defined) |
Metric does not affect scoring and will be ignored |
||
UC (Unconfirmed) For cvssMetricV2 |
There are isolated, unverified reports |
||
UR (Uncorroborated) For cvssMetricV2 |
Multiple sources generally describe the vulnerability |
||
R (Reasonable) For cvssMetricV3 |
Vulnerability reports describe the root cause |
||
U (Unconfirmed) |
Reports lack a description of the vulnerability root cause |
||
Environmental Metrics |
CR (Confidentiality Requirement) |
H (High) |
Loss of confidentiality would have a catastrophic impact |
M (Medium) |
Loss of confidentiality would have a serious impact |
||
L (Low) |
Loss of confidentiality would have a limited impact |
||
PD/X (Not Defined |
Metric does not affect scoring and will be ignored |
||
IR (Integrity Requirement) |
H (High) |
Integrity violation would have a catastrophic impact |
|
M (Medium) |
Integrity violation would have a serious impact |
||
L (Low) |
Integrity violation would have a limited impact |
||
PD/X (Not Defined) |
Metric does not affect scoring and will be ignored |
||
AR (Availability Requirement) |
H (High) |
Loss of availability would have a catastrophic impact |
|
M (Medium) |
Loss of availability would have a serious impact |
||
L (Low) |
Loss of availability would have a limited impact |
||
MAV (Modified Attack Vector), MAC (Modified Attack Complexity), MPR (Modified Privileges Required), MUI (Modified User Interaction), MS (Modified Scope) Modified impact metrics adjusted for the specific environment |
|||